A Computer Incident Report (CIR) is a crucial document for documenting security incidents that have occurred within an organization’s IT systems. It serves as a record of the event, its impact, and the steps taken to address it. A well-structured CIR is essential for legal compliance, incident response, and continuous improvement of security posture. This article provides a comprehensive guide to creating and utilizing a robust Computer Incident Report Template. Understanding the purpose and proper format of a CIR is paramount for effectively managing security risks and minimizing potential damage. The core of a successful CIR lies in its clarity, accuracy, and thoroughness. It’s not just a report; it’s a communication tool. Computer Incident Report Template – a standardized format ensures consistent documentation and facilitates efficient investigations. This guide will walk you through each section, offering practical advice and best practices.
Understanding the Importance of Computer Incident Reports
The rise of cyber threats has dramatically increased the need for proactive security measures. A Computer Incident Report (CIR) is a vital component of this strategy. It provides a chronological account of security events, allowing organizations to:
- Identify and Analyze Threats: CIRs help pinpoint the root cause of incidents, revealing vulnerabilities and attack vectors.
- Meet Regulatory Requirements: Many regulations (e.g., GDPR, HIPAA, PCI DSS) require documented incident response plans and reporting.
- Support Legal Investigations: A clear CIR provides essential evidence for legal proceedings and investigations.
- Improve Security Posture: Analyzing past incidents through CIRs allows organizations to identify weaknesses and implement corrective actions.
- Enhance Incident Response: The CIR serves as a foundation for effective incident response plans, streamlining the recovery process.
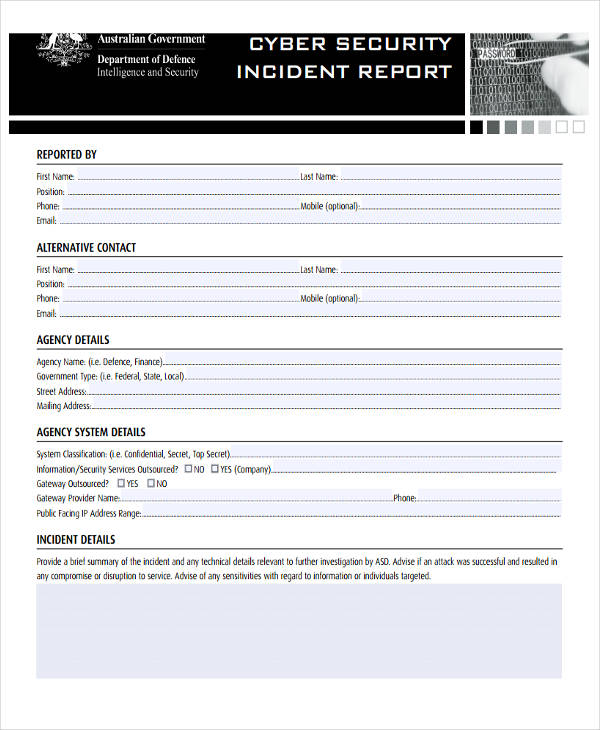
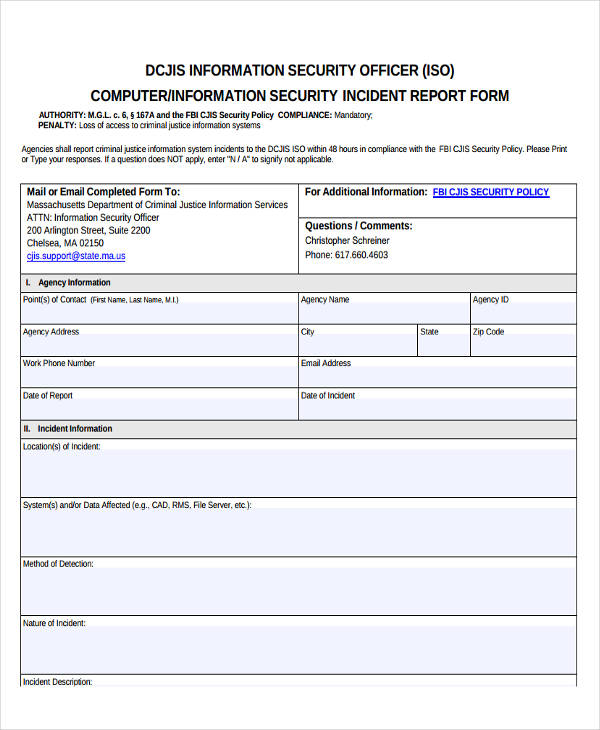
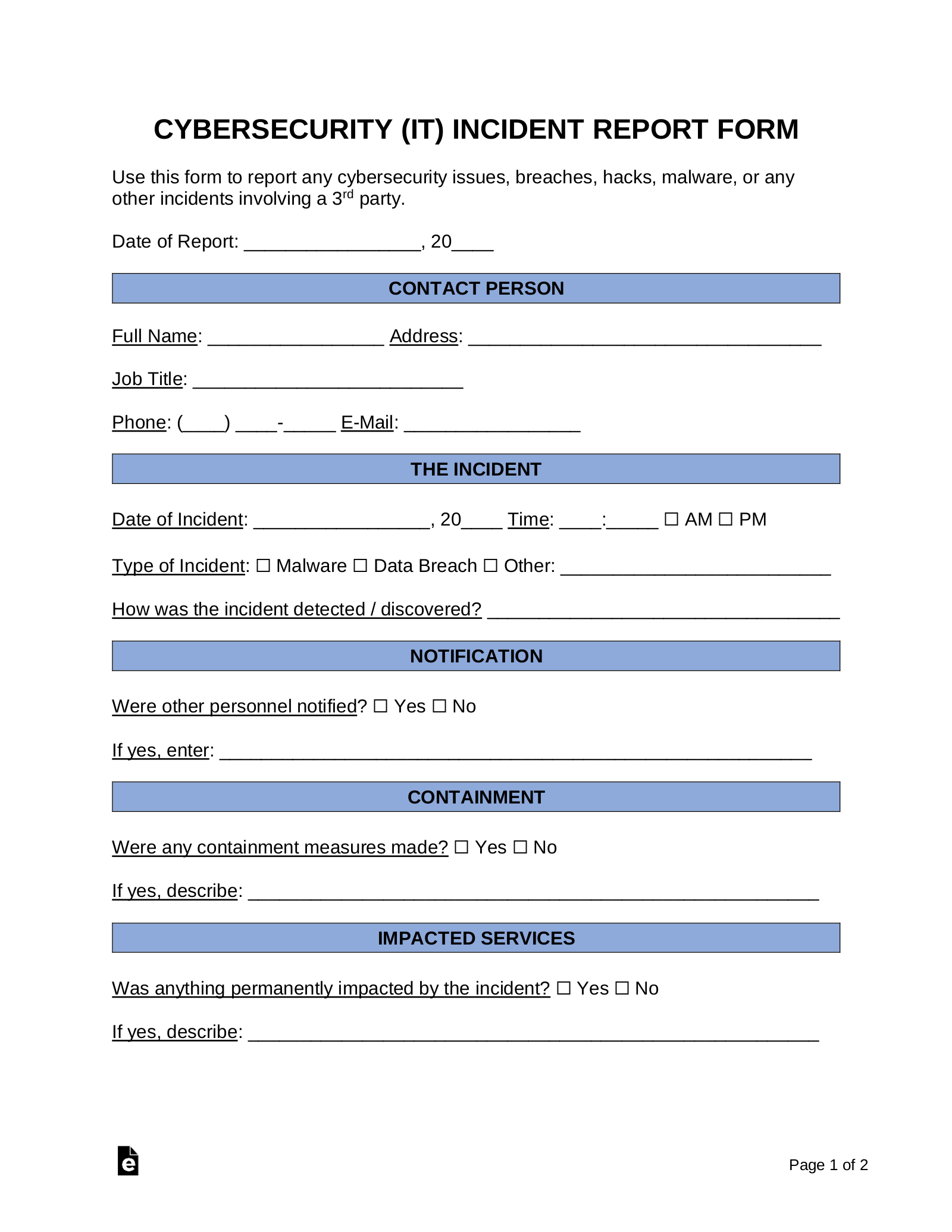
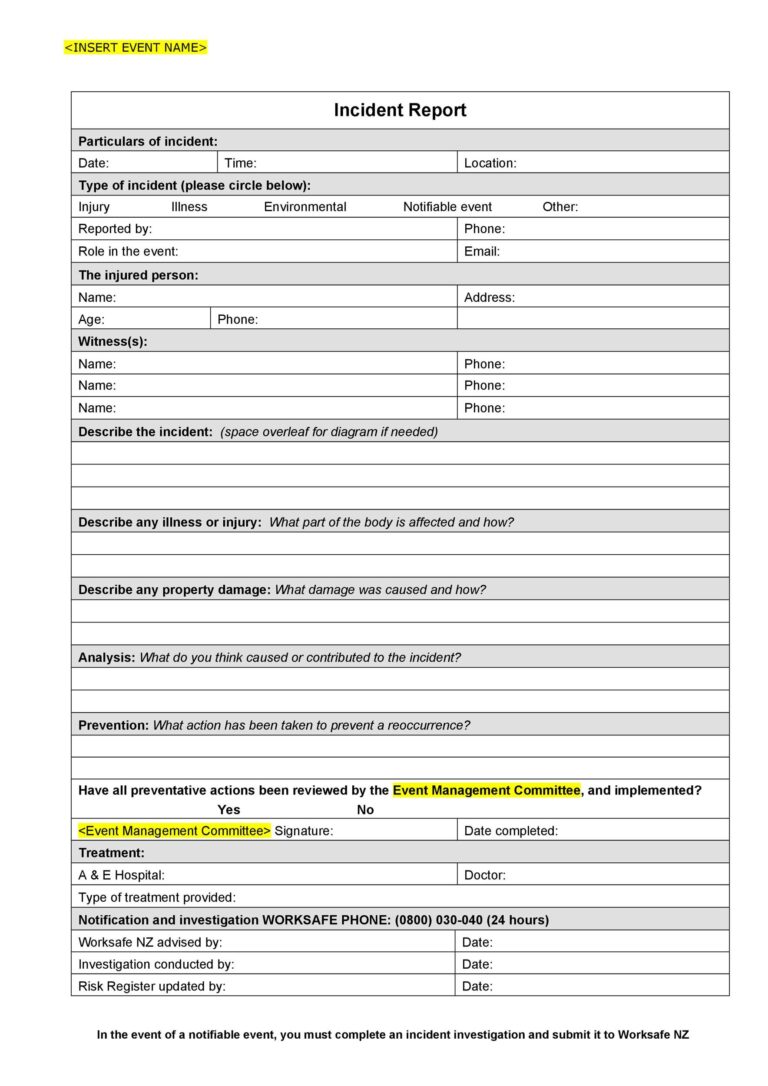
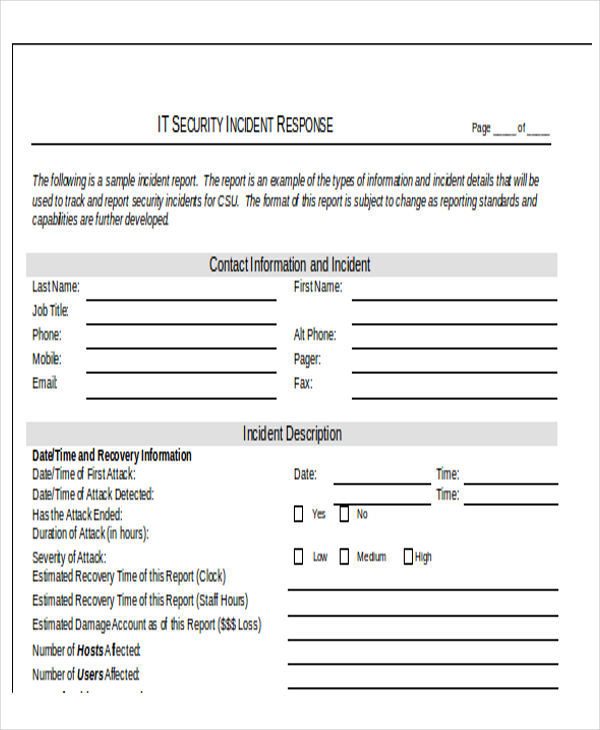
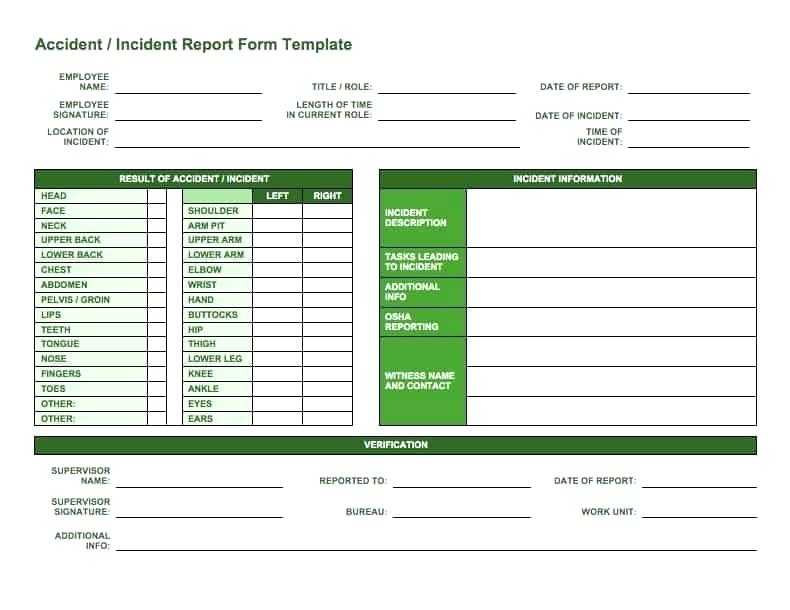
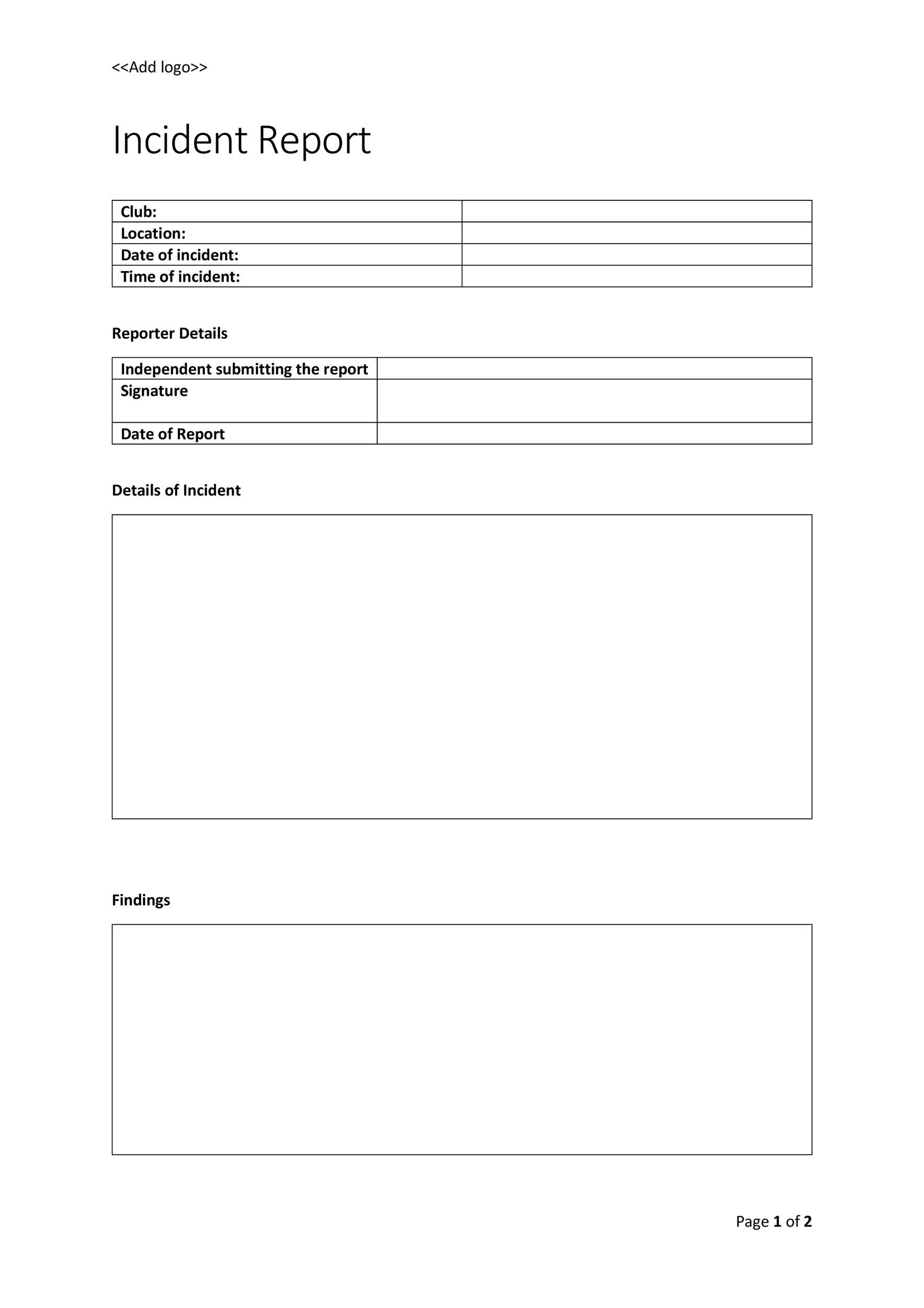
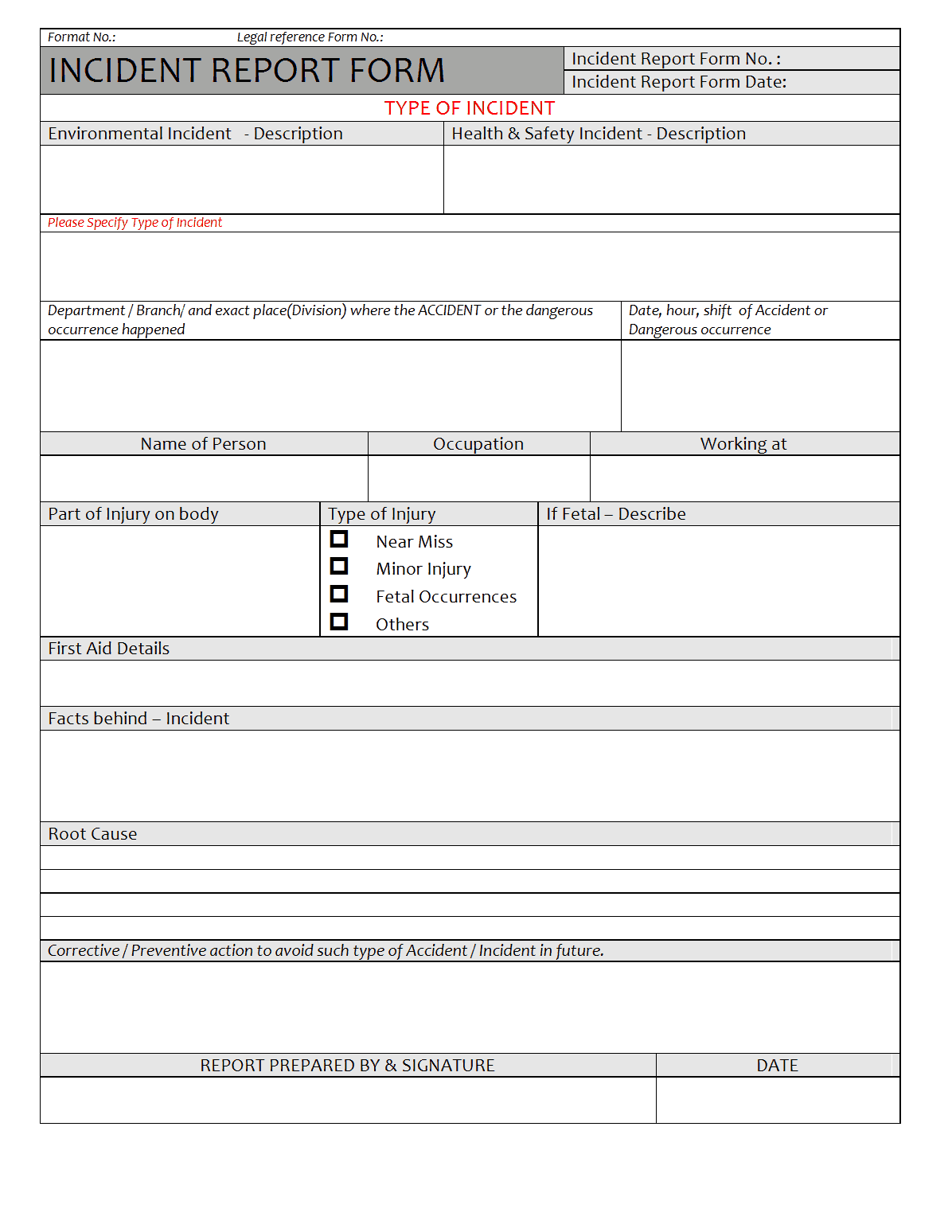
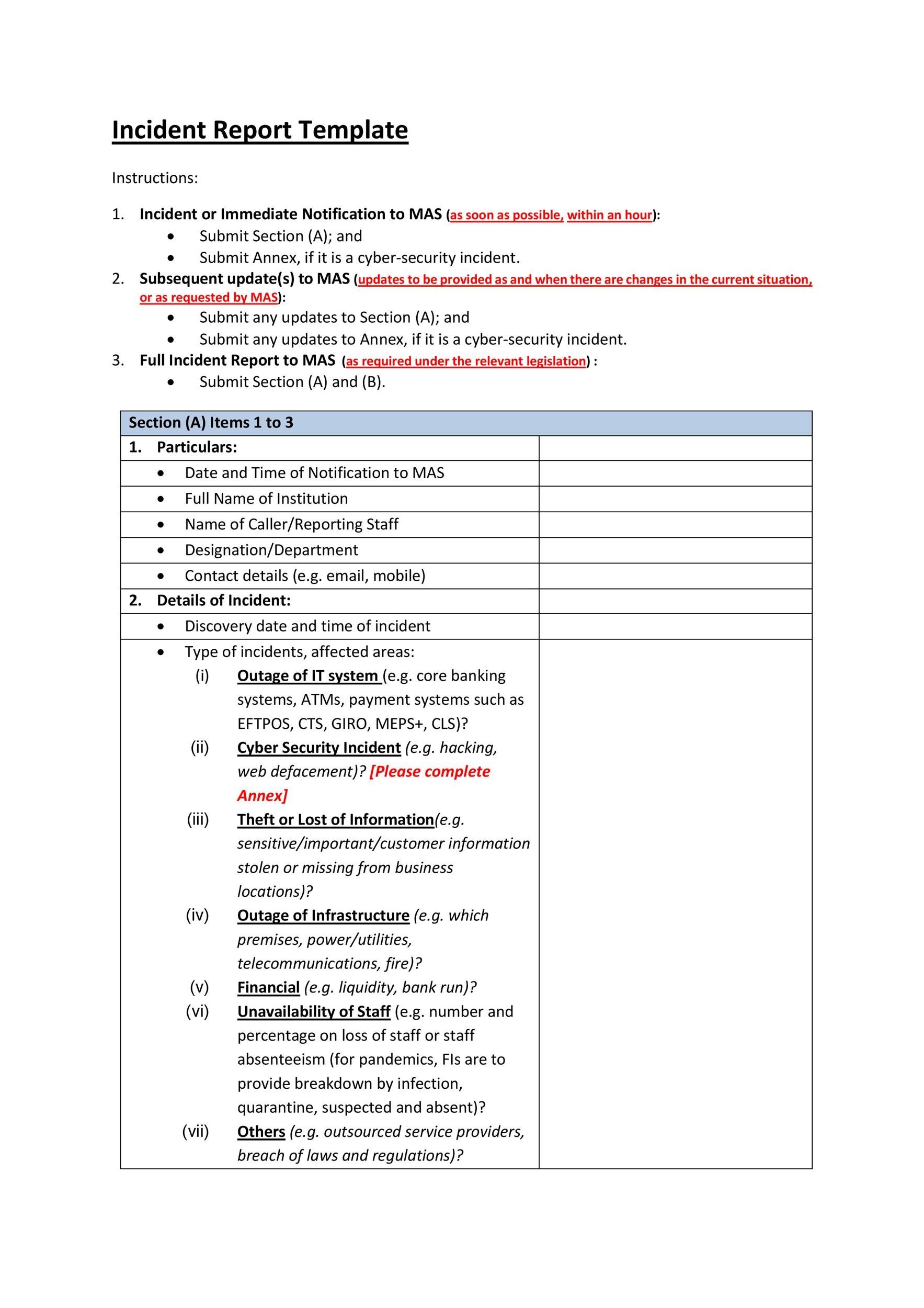
The Core Components of a Computer Incident Report Template
A well-structured Computer Incident Report Template typically includes the following sections:
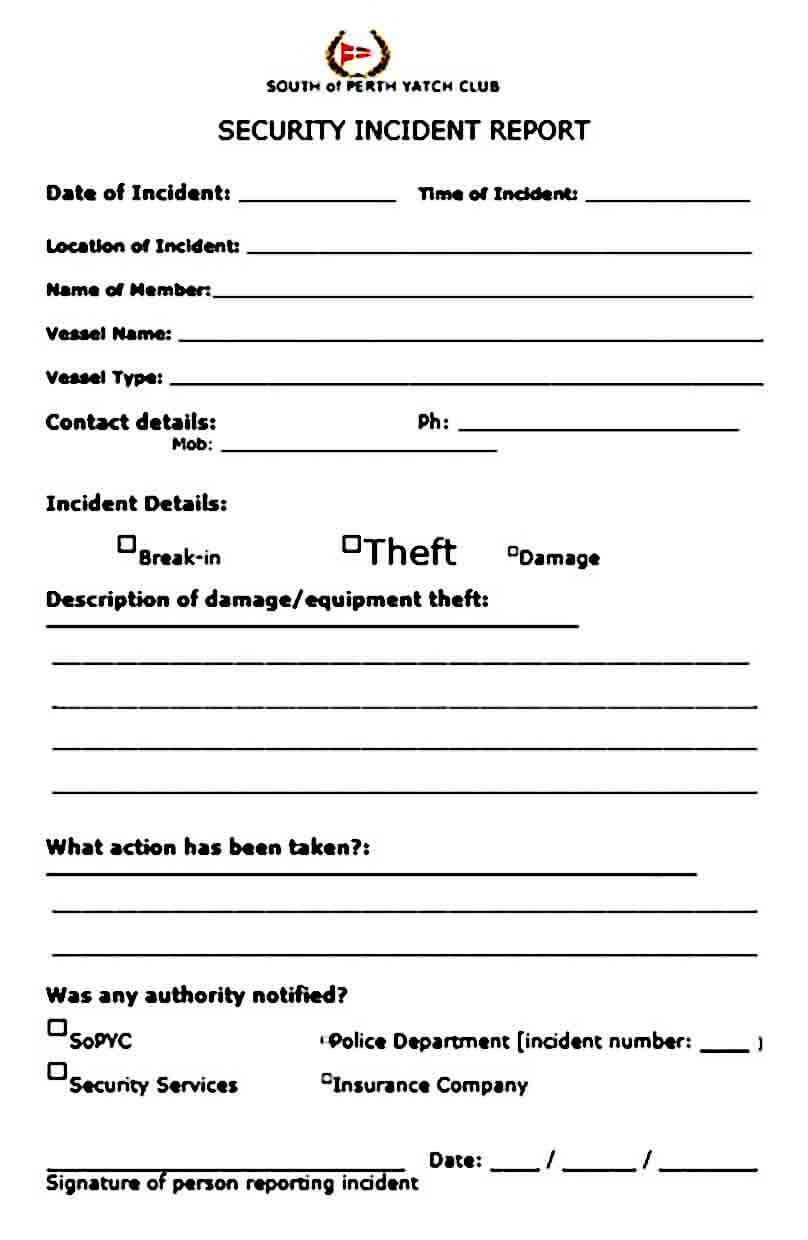
- Incident Summary
- Date and Time of Incident
- Reporting Party
- Affected Systems/Data
- Description of Incident
- Impact Assessment
- Containment Actions Taken
- Recovery Actions Taken
- Root Cause Analysis
- Lessons Learned
Section 1: Incident Summary
This section provides a concise overview of the incident. It should include the following:
- Incident Type: Clearly identify the type of incident (e.g., malware infection, phishing attack, data breach, unauthorized access).
- Date and Time of Occurrence: Record the precise date and time the incident was detected.
- Brief Description: Summarize the incident in a few sentences – what happened, who was affected, and what systems were involved. This is a critical section for capturing the essence of the event.
- Initial Alert/Notification: Document any alerts or notifications received prior to the incident being reported.
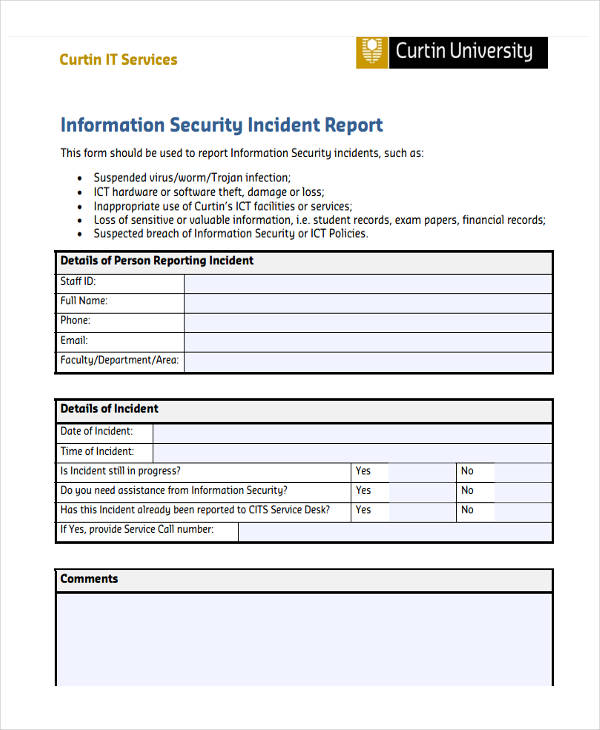
Section 2: Reporting Party
This section identifies the individual or team responsible for reporting the incident. Include:
- Name and Contact Information: Provide the full name, title, and contact details of the reporter.
- Department/Team: Specify the department or team responsible for the incident.
- Authorization: Note any approvals or authorizations required for reporting the incident.
Section 3: Affected Systems/Data
This section details the systems and data that were impacted by the incident. Be specific:
- System Names: List all affected systems (e.g., servers, workstations, databases, cloud services).
- Affected Data: Identify the specific data that was compromised or accessed (e.g., customer records, financial data, intellectual property). Categorize the data if possible (e.g., Personally Identifiable Information (PII), Protected Health Information (PHI)).
- Data Sensitivity Level: Assess the sensitivity level of the affected data (e.g., Confidential, Restricted, Public).
Section 4: Description of Incident
This is the most detailed section, providing a narrative of the incident. It should include:
- Step-by-Step Account: Chronologically describe the events leading up to, during, and after the incident.
- User Actions: Document the actions of individuals involved in the incident (e.g., clicking on a malicious link, opening an infected email attachment).
- Technical Details: Include relevant technical information, such as error messages, logs, and network traffic data. Avoid overly technical jargon unless necessary.
- Evidence: Document any evidence collected, such as screenshots, logs, and forensic images.
Section 5: Impact Assessment
This section assesses the consequences of the incident. It should include:
- Business Impact: Evaluate the potential impact on business operations (e.g., financial losses, reputational damage, legal liabilities).
- System Downtime: Estimate the duration of any system downtime caused by the incident.
- Data Loss: Determine the extent of data loss or corruption.
- Security Remediation Efforts: Document any steps taken to contain the incident and remediate the vulnerabilities that were exploited.
Section 6: Containment Actions Taken
This section details the steps taken to contain the incident and prevent further damage. Include:
- Immediate Actions: Describe the initial actions taken to isolate the affected systems.
- Firewall Rules: Document any changes made to firewall rules.
- Network Segmentation: Describe any network segmentation implemented.
- System Isolation: Document any system isolation measures taken.
Section 7: Recovery Actions Taken
This section outlines the steps taken to restore systems and data to normal operation. Include:
- System Restoration: Describe the process of restoring systems from backups.
- Data Recovery: Document the process of recovering data from backups or other sources.
- Patching: Document any patches applied to affected systems.
- Verification: Verify the integrity of restored systems and data.
Section 8: Root Cause Analysis
This section investigates the underlying cause of the incident. It should include:
- Potential Causes: Identify potential causes of the incident (e.g., software vulnerability, phishing attack, human error).
- Vulnerability Assessment: Assess the vulnerability that was exploited.
- Root Cause Diagram: Create a visual representation of the root cause.
Section 9: Lessons Learned
This section summarizes the key takeaways from the incident. Include:
- What Went Well: Document successes and positive outcomes.
- What Could Be Improved: Identify areas for improvement in security practices and incident response procedures.
- Recommendations: Provide specific recommendations for preventing similar incidents in the future.
Conclusion
Computer Incident Reports are an indispensable tool for organizations seeking to protect their assets and maintain a strong security posture. By following a structured approach and diligently documenting each step of the incident response process, organizations can effectively manage security risks, minimize damage, and improve their overall resilience. A well-crafted CIR is not merely a document; it’s a proactive measure that safeguards the organization’s future. Computer Incident Report Template – consistently utilizing this template will significantly enhance your organization’s ability to respond effectively to and learn from security incidents.
Additional Resources
- Link to NIST Cybersecurity Framework
- Link to SANS Institute Incident Response Guide
- Link to various cybersecurity blogs and articles