The world of digital security relies heavily on robust and reliable Certificate Authority (CA) solutions. These CA’s are the trusted intermediaries that issue digital certificates, verifying the identity of websites, individuals, and organizations. Choosing the right CA template is a critical decision for any organization seeking to establish a secure online presence. This article will delve into the world of Certificate Authority Templates, exploring different types, features, and considerations for selecting the most suitable option for your specific needs. Understanding the nuances of these templates is essential for ensuring your digital infrastructure remains secure and compliant. Certificate Authority Templates are more than just software; they represent a strategic investment in your organization’s security posture.
The rise of cloud computing and the increasing reliance on remote access have dramatically increased the importance of secure digital identities. Without proper certificate management, organizations are vulnerable to phishing attacks, man-in-the-middle threats, and other malicious activities. A well-designed Certificate Authority Template provides a foundational layer of security, verifying the authenticity of users and devices before granting access to sensitive resources. The effectiveness of a CA template hinges on its ability to handle a wide range of certificate types, manage key lifecycle, and integrate seamlessly with existing security systems. Let’s explore the different types of Certificate Authority Templates available and how to choose the best fit for your organization.
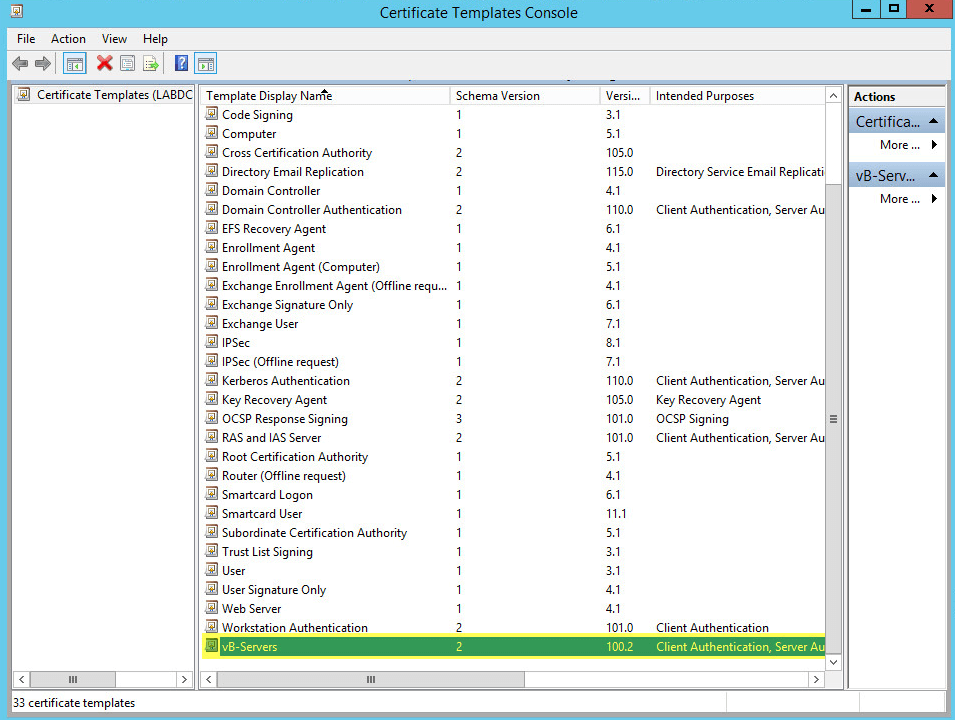
Understanding the Different Types of Certificate Authority Templates
Several distinct types of Certificate Authority Templates cater to varying needs and technical capabilities. Each offers a unique set of features and functionalities. Here’s a breakdown of some of the most common types:
1. Cloud-Based Templates
Cloud-based CA templates are increasingly popular due to their scalability, ease of deployment, and reduced operational overhead. These templates are hosted on a cloud platform, allowing for easy access and management. They typically offer features like automated key rotation, multi-factor authentication (MFA), and integration with identity providers. Cloud-based Templates are particularly well-suited for organizations with limited IT resources or those seeking a highly scalable solution. They often provide a simplified interface for managing certificates and key pairs, reducing the complexity of certificate lifecycle management. However, they can be more expensive than on-premise solutions.
2. On-Premise Templates
On-premise CA templates are installed and managed within an organization’s own data center. This approach offers greater control over data security and compliance, but it also requires significant upfront investment in hardware, software, and IT expertise. These templates typically provide a wider range of customization options and are often preferred by organizations with stringent regulatory requirements. On-Premise Templates are a good choice for organizations that prioritize complete control over their certificate infrastructure and have the resources to manage it effectively. They often include advanced features like granular control over certificate issuance and revocation.
3. Hybrid Templates
Hybrid templates represent a blend of cloud and on-premise approaches. They allow organizations to leverage the benefits of both models, distributing some certificate management tasks to the cloud while maintaining control over sensitive data and operations within their own infrastructure. This approach is becoming increasingly common as organizations seek a flexible and scalable solution. Hybrid Templates offer a balance between cost, control, and ease of management.
Key Features to Consider When Selecting a Certificate Authority Template
Beyond the type of template, several key features should be carefully evaluated when selecting a CA solution. These features directly impact the security, usability, and overall effectiveness of your certificate management system.
- Key Management: Robust key management is paramount. The template should provide secure key storage, rotation, and revocation mechanisms. Consider features like HSM (Hardware Security Modules) integration for enhanced security.
- Certificate Issuance: The ability to issue certificates quickly and efficiently is crucial. Look for templates that support automated certificate issuance workflows and integration with existing identity providers.
- Certificate Revocation: A reliable certificate revocation process is essential for mitigating the risk of compromised certificates. The template should provide mechanisms for automated revocation and monitoring.
- Multi-Factor Authentication (MFA): Integrating MFA is a critical security best practice. Ensure the template supports MFA for both certificate issuance and key management.
- Compliance Support: If your organization operates in a regulated industry (e.g., finance, healthcare), verify that the template supports relevant compliance standards (e.g., PCI DSS, HIPAA).
- Reporting and Auditing: Comprehensive reporting and auditing capabilities are essential for monitoring certificate activity and identifying potential security issues.
Integrating Certificate Authority Templates with Existing Security Systems
Choosing the right Certificate Authority Template is only half the battle. Successful implementation requires careful integration with existing security systems. Consider the following:
- Identity Providers (IdPs): Seamless integration with IdPs like Active Directory, Azure AD, or Okta is crucial for automating certificate provisioning and management.
- Endpoint Security: Ensure the template integrates with endpoint security solutions to enforce certificate validation and prevent compromised devices from issuing invalid certificates.
- Security Information and Event Management (SIEM): Integrate the template with your SIEM system to provide real-time monitoring and alerting for suspicious certificate activity.
- Vulnerability Management: Consider how the template integrates with your vulnerability management system to ensure that certificates are regularly scanned for vulnerabilities.
Best Practices for Certificate Authority Template Implementation
To maximize the benefits of your Certificate Authority Template, consider the following best practices:
- Regular Security Audits: Conduct regular security audits of your certificate management system to identify and address potential vulnerabilities.
- Employee Training: Provide comprehensive training to your IT staff on certificate management best practices.
- Incident Response Plan: Develop an incident response plan to address potential certificate-related security incidents.
- Version Control: Maintain strict version control of your certificate templates to ensure compatibility and prevent errors.
- Continuous Monitoring: Continuously monitor your certificate infrastructure for anomalies and potential security threats.
Conclusion: Securing Your Digital Identity with Certificate Authority Templates
Selecting the appropriate Certificate Authority Template is a strategic decision that can significantly impact your organization’s security posture. By carefully considering your organization’s specific needs, technical capabilities, and regulatory requirements, you can choose a template that provides a robust and reliable foundation for secure digital identities. Certificate Authority Templates are no longer a luxury; they are a necessity for organizations seeking to protect their assets and maintain a strong reputation. Investing in the right solution now will save you significant time, money, and potential risks in the long run. Ultimately, a well-implemented Certificate Authority Template is a cornerstone of a secure and resilient digital environment.