The rise of mobile technology has fundamentally changed how we connect, communicate, and access information. However, this increased reliance on wireless connectivity – particularly guest Wi-Fi – presents both opportunities and challenges. A robust and clearly defined Guest Wireless Acceptable Use Policy Template is crucial for protecting your business, ensuring fair access for all users, and mitigating potential risks. This template provides a framework for establishing guidelines regarding acceptable use of the wireless network, safeguarding your assets, and maintaining a positive user experience. It’s more than just a policy; it’s a proactive measure demonstrating your commitment to responsible technology usage. This document aims to offer a comprehensive and adaptable solution for businesses of all sizes.
Understanding the Importance of a Policy
Before diving into the specifics of the Guest Wireless Acceptable Use Policy Template, it’s important to understand why it’s so vital. Without a clear policy, you risk:
- Data Breaches: Uncontrolled access to the network can expose sensitive business data to unauthorized individuals.
- Security Risks: Malicious users can exploit vulnerabilities to disrupt services, steal information, or even cause damage to equipment.
- Legal Liabilities: Failure to adequately protect your network can lead to legal repercussions, particularly in cases of data breaches or privacy violations.
- Reputational Damage: A security incident can severely damage your brand’s reputation and erode customer trust.
- Operational Disruptions: Uncontrolled usage can lead to network congestion, slow speeds, and overall service degradation.
A well-crafted Guest Wireless Acceptable Use Policy Template acts as a critical defense against these risks, establishing a baseline for acceptable behavior and promoting responsible technology use. It’s a foundational element of a comprehensive IT security strategy.
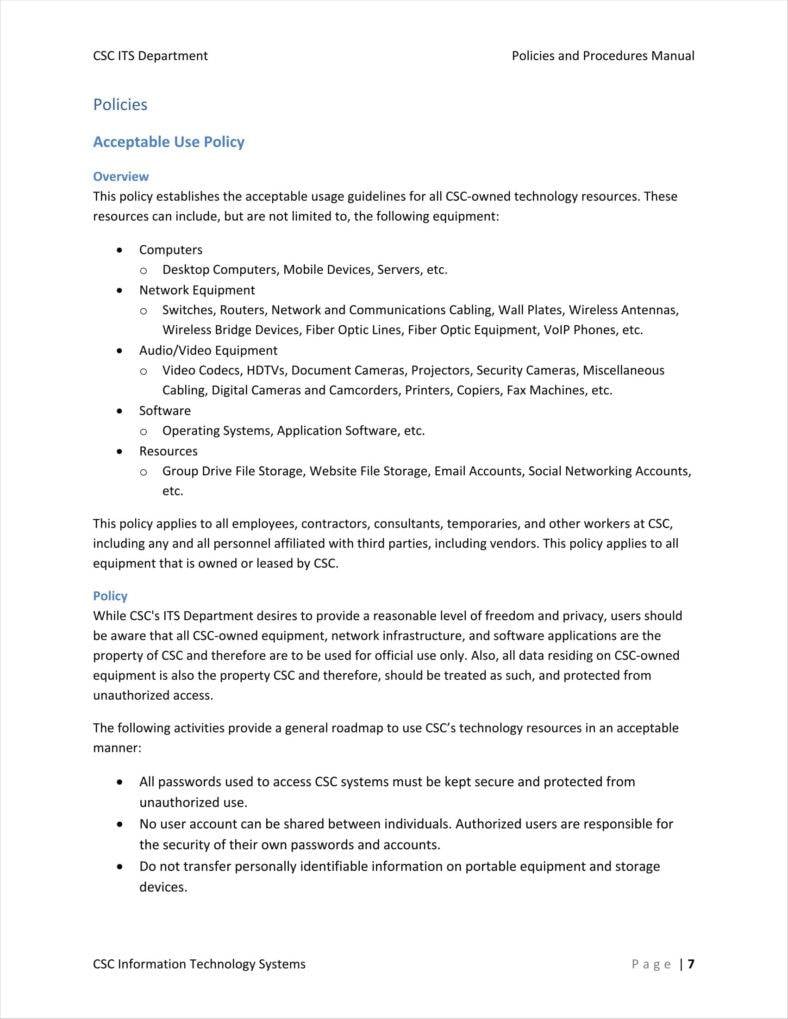
Key Components of a Robust Policy
A comprehensive Guest Wireless Acceptable Use Policy Template should address several key areas:
- Network Access: Define who is permitted to connect to the wireless network. This typically includes employees, contractors, and visitors.
- Acceptable Use: Clearly outline what constitutes acceptable use of the network. This includes activities like browsing the internet, sending emails, downloading files, and using social media.
- Data Security: Emphasize the importance of protecting company data. This includes password protection, secure file sharing, and avoiding suspicious downloads.
- Device Usage: Specify rules regarding the types of devices allowed on the network (e.g., smartphones, tablets, laptops).
- Wi-Fi Security: Detail the security protocols in place, such as encryption (WPA2 or WPA3) and password requirements.
- Monitoring & Enforcement: Explain how the network will be monitored and how violations will be addressed. This might include logging activity or contacting users.
- Guest Restrictions: Clearly state any restrictions on guest access, such as limitations on usage time or data transfer.
Detailed Policy Sections – A Template
Let’s examine some key sections of a Guest Wireless Acceptable Use Policy Template in more detail:
1. Network Access & Permissions
This section establishes who is allowed to connect to the wireless network. It’s crucial to clearly define roles and responsibilities. For example:
- Employees: All employees are permitted to connect to the network for business purposes. They are responsible for adhering to the policy and reporting any security concerns.
- Contractors: Contractors are typically granted access to the network for specific projects, subject to approval from IT.
- Visitors: Visitors are generally restricted from accessing the network unless specifically authorized. A visitor agreement should be signed upon arrival.
The policy should also address the process for requesting access to the network.
2. Acceptable Use Guidelines
This section provides a detailed explanation of what is considered acceptable use. It’s important to be specific and avoid ambiguity.
- Internet Browsing: Users are permitted to browse the internet for educational or personal purposes. Excessive or inappropriate browsing is discouraged.
- Email Communication: Email communication is permitted, but users are responsible for maintaining a professional tone and adhering to company email etiquette.
- Downloading and Uploading Files: Downloading and uploading files are permitted, but users must ensure that files are not distributed to unauthorized individuals.
- Social Media: Social media use is generally permitted, but users should be mindful of the potential for inappropriate content and privacy concerns.
3. Data Security Measures
Protecting company data is paramount. This section outlines specific security measures:
- Password Protection: All devices must have strong, unique passwords. Password management tools are encouraged.
- Secure File Sharing: File sharing should be conducted through secure channels, such as a dedicated file server or cloud storage.
- Avoid Suspicious Downloads: Users should avoid downloading files from untrusted sources.
- Reporting Security Concerns: Users are encouraged to report any suspected security breaches or suspicious activity to IT support.
4. Wi-Fi Security Protocols
The security of the wireless network is critical. This section details the protocols used to secure the network:
- Encryption: WPA2 or WPA3 encryption is required to protect data transmitted over the network.
- Password Protection: A strong, unique password is required to access the network.
- Guest Network: A separate guest network should be established to isolate guest devices from the company network.
5. Monitoring and Enforcement
How will the policy be enforced? This section outlines the monitoring process:
- Logging: Network activity will be logged to detect potential security breaches.
- Reporting: Users will be notified of any violations of the policy.
- Consequences: Violations of the policy may result in disciplinary action, up to and including termination of employment or contract.
Conclusion
A well-crafted Guest Wireless Acceptable Use Policy Template is an essential investment for any organization that relies on wireless connectivity. By establishing clear guidelines and promoting responsible technology usage, you can significantly reduce the risks associated with guest Wi-Fi networks, protect your data, and maintain a positive user experience. Regular review and updates of the policy are crucial to keep pace with evolving security threats and technological advancements. Ultimately, a proactive approach to network security is a key component of a successful and sustainable IT strategy. Remember to tailor the policy to your specific business needs and industry regulations.